Built for innovation,
trusted by businesses
worldwide by results
We combine scalable technology, enhanced security, and an intuitive interface to ensure your team can work efficiently and confidently. trusted by teams worldwide,
Scalable Solutions
Enhanced Security
User-Friendly Interface
End-to-End infrastructure for Training, Scaling, and Serving AI Models
Cloud-Based Solutions
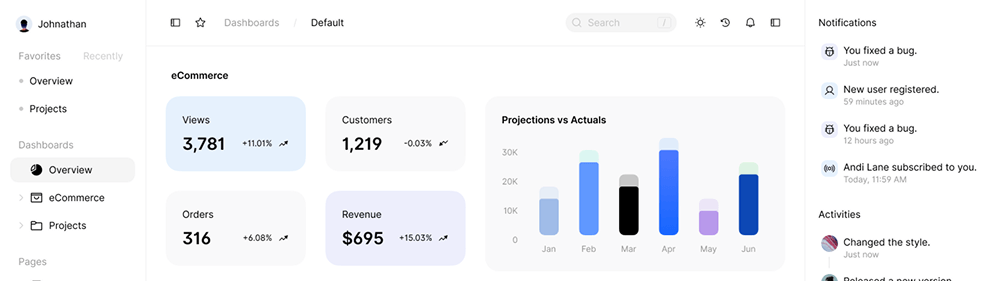
Data Analytics & Report
Data-Driven Intelligence
API Integrations
Security & Compliance
Multi-Device Access
AI-Powered Services
Support & Maintenance
All-in-one tools built for growth, performance, & efficiency
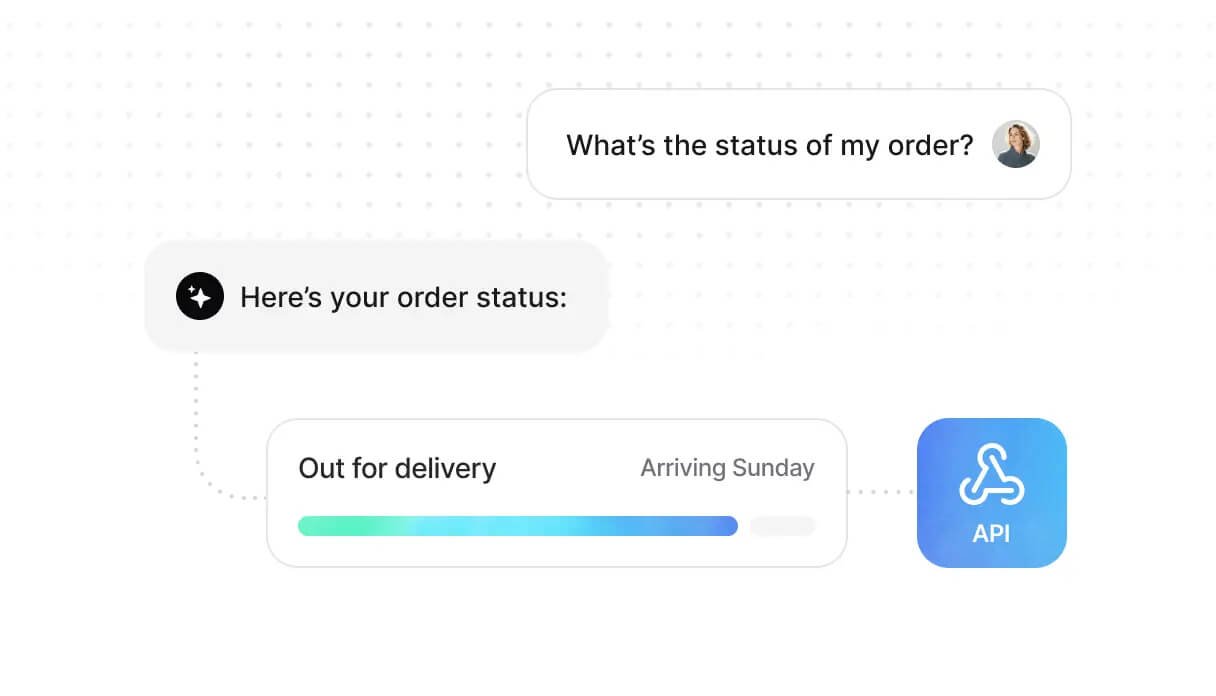
Sync with real-time data
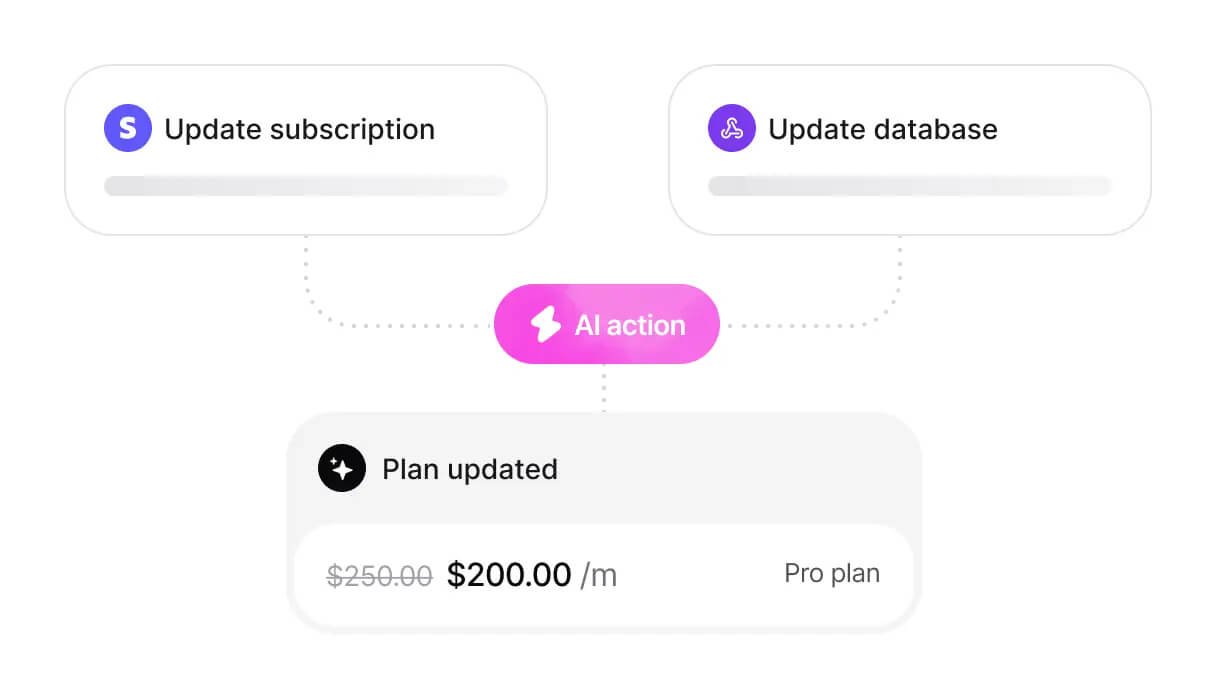
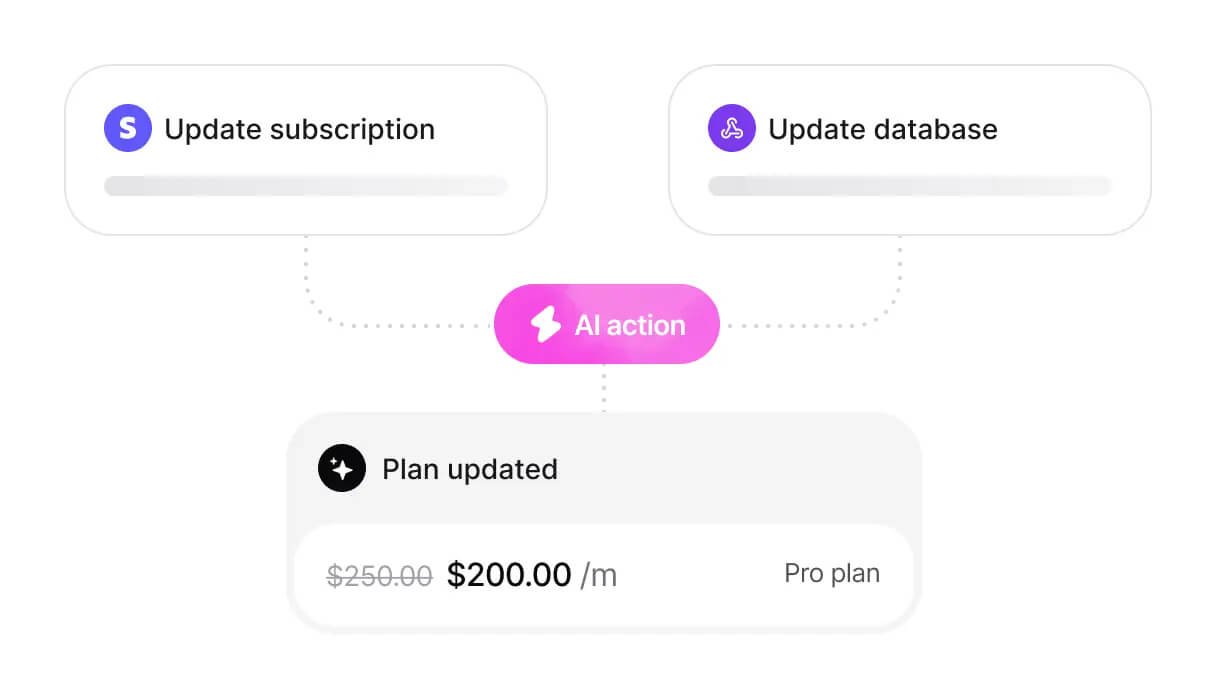
Take actions on your systems
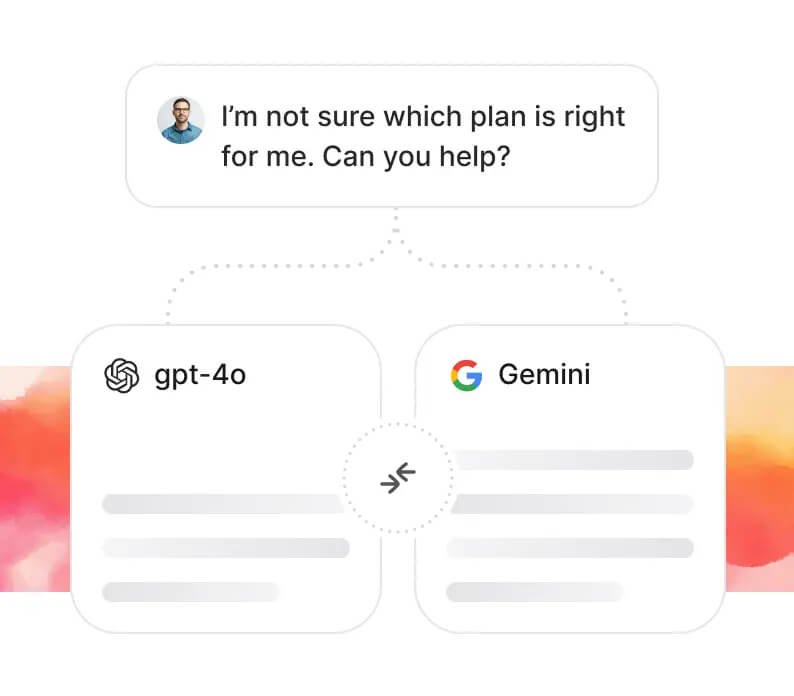
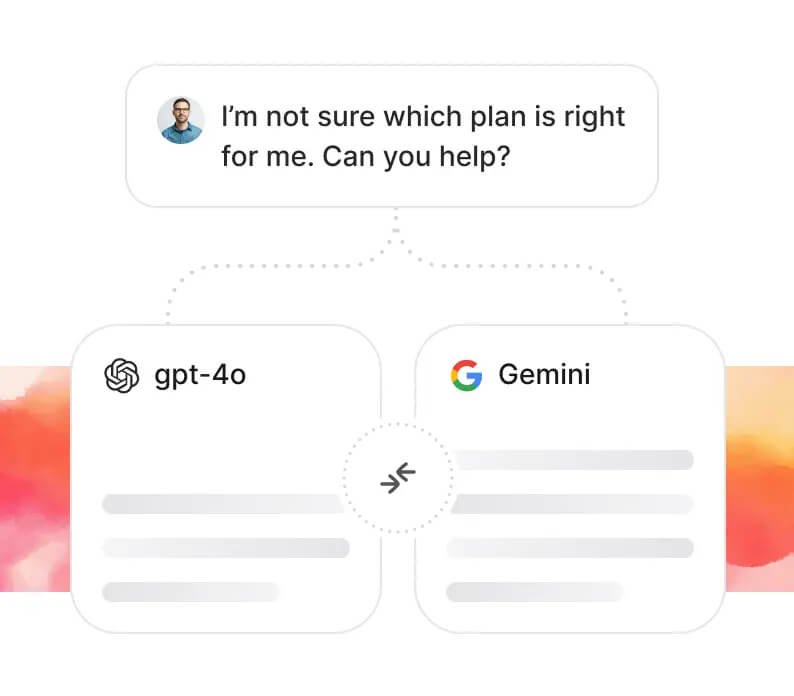
Compare AI models
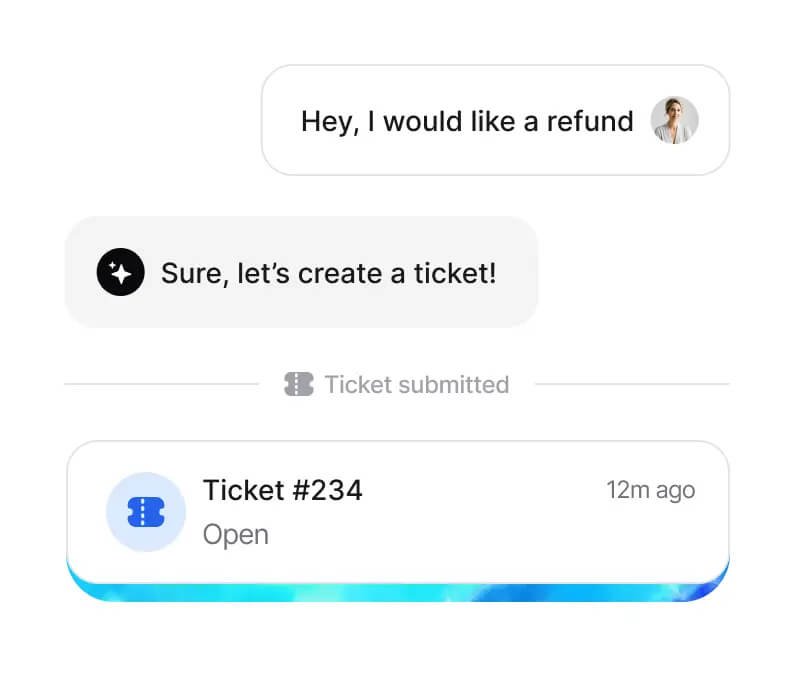
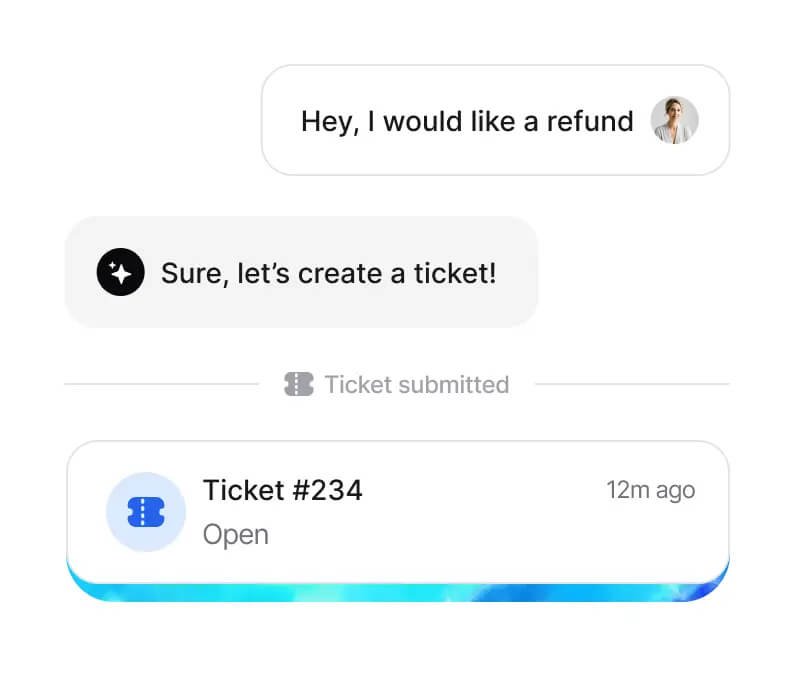
Smart escalation
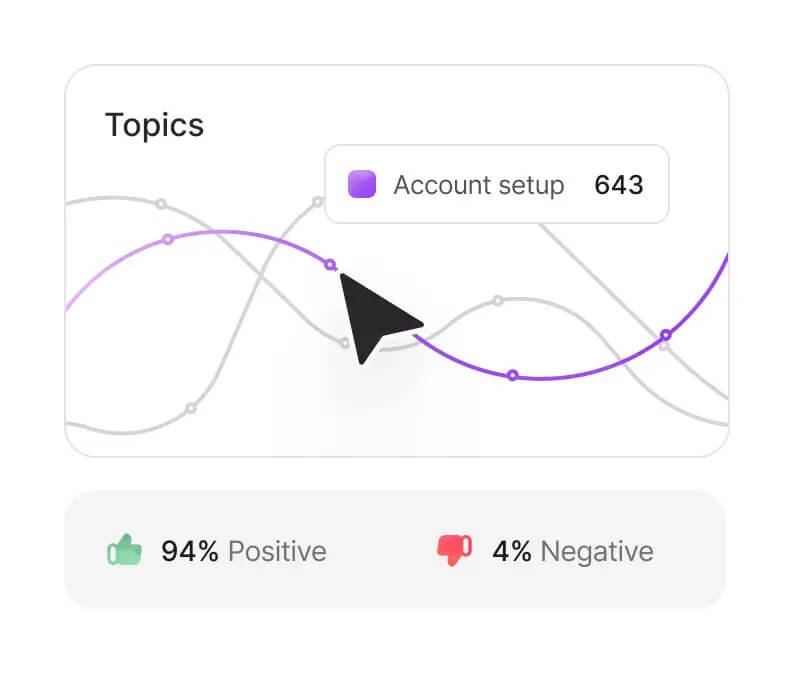
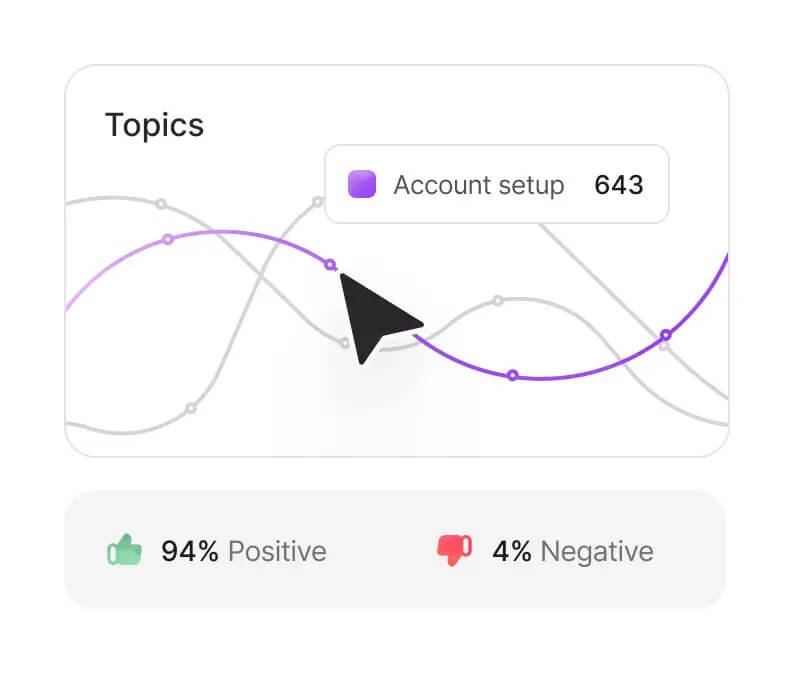
Advanced reporting
Frequently asked questions
Have questions? We’ve got answers. Our frequently asked questions cover everything you need to know about our platform.
1. What is your SaaS platform?
We use enterprise-grade security protocols, including end-to-end encryption, role-based access, and compliance
2. How secure is your platform?
We use enterprise-grade security protocols, including end-to-end encryption, role-based access, and compliance
3. Can I try the platform before subscribing?
We use enterprise-grade security protocols, including end-to-end encryption, role-based access, and compliance
4. Is the platform scalable for growing businesses?
We use enterprise-grade security protocols, including end-to-end encryption, role-based access, and compliance
5. What kind of customer support do you offer?
We use enterprise-grade security protocols, including end-to-end encryption, role-based access, and compliance
Seamless setup, instant heigh Productivity